How AI is helping cut the risks of breaches with patch management
AI/ML-driven patch management delivers real-time risk assessments, guiding IT and security teams to prioritize critical patches first. …
Join our daily and weekly newsletters for the latest updates and exclusive content on industry-leading AI coverage. Learn More
When it comes to patching endpoints, systems and sensors across an enterprise, complacency kills.
For many IT and security teams, it’s a slow burn of months of seven-day weeks trying to recover from a breach that could have been avoided.
For CISOs and CIOs, it’s a credibility hit to their careers for allowing a breach on their watch that could have been avoided. And for the board and the CEO, there’s the accountability they have to own for a breach, especially if they’re a publicly traded U.S. company.
Attackers’ arsenals are getting better at finding unpatched systems
There’s a booming market on the dark web for the latest kits and tools to identify systems and endpoints that aren’t patched correctly and have long-standing Common Vulnerabilities and Exposures (CVEs).
I.P. scanners and exploit kits designed to target specific CVEs associated with widely used software across enterprises are sold on the dark web by cybercriminals. Exploit kits are constantly updated with new vulnerabilities, a key selling point to attackers looking to find systems that lack current patches to stay protected.
CYFIRMA confirms that it has found exploit kits for popular software, including Citrix ADC, Microsoft Streaming Service Proxy and PaperCut. However, its research also finds that offering patches after a major CVE breach is only somewhat effective.
Attackers continue to exploit long-known vulnerabilities in CVEs, knowing there’s a good chance that organizations that have vulnerable CVEs haven’t patched them in a year or more. A recent report finds that 76% of vulnerabilities currently being exploited by ransomware groups were first discovered between 2010 and 2019.
Unpatched systems are open gateways to devastating cyberattacks
VentureBeat has learned of small and mid-tier midwestern U.S. manufacturers having their systems hacked because security patches were never installed. One had their Accounts Payable systems hacked with attackers redirecting ACH accounts payable entries to funnel all payments to rogue, untraceable offshore accounts.
It’s not just manufacturers getting hit hard with cyberattacks that start with patches being out of date or not installed at all. On May 13, the city of Helsinki, Finland, suffered a data breach because attackers exploited an unpatched vulnerability in a remote access server.
The infamous Colonial Pipeline ransomware attack was attributed to an unpatched VPN system that also didn’t have multifactor authentication enabled. Attackers used a compromised password to gain access to the pipeline’s network through an unpatched system.
Nation-state attackers have the extra motivation of keeping “low and slow” attacks undiscoverable so they can achieve their espionage goals, including spying on senior executives’ emails as Russian attackers did inside Microsoft, stealing new technologies or source code that can go on for months or years is common.
A quick first win: get IT and security on the same page with the same urgency
Ivanti’s most recent state of cybersecurity report finds that 27% of security and IT departments are not aligned on their patching strategies and 24% don’t agree on patching cycles. When security and IT are not on the same page, it makes it even more challenging for overworked IT and security teams to make patch management a priority.
Six in ten breaches are linked to unpatched vulnerabilities. The majority of IT leaders responding to a Ponemon Institute survey, 60%, say that one or more of the breaches potentially occurred because a patch was available for a known vulnerability but not applied in time.
IT and security teams put off patch management until there’s an intrusion or breach attempt. Sixty-one percent of the time, an external event triggers patch management activity in an enterprise. Being in react mode, IT teams already overwhelmed with priorities push back on other projects that may have revenue potential. Fifty-eight percent of the time, it’s an actively exploited vulnerability that again pushes IT into a reactive mode of fixing patches. Seventy-one percent of IT and security teams say it is overly complex, cumbersome and time-consuming.
Fifty-seven percent of those same IT and cybersecurity professionals say remote work and decentralized workspaces make patch management even more challenging.
Patch management vendors fast-tracking AI/ML and risk-based management
AI/machine learning (ML)-driven patch management delivers real-time risk assessments, guiding IT and security teams to prioritize the most critical patches first.
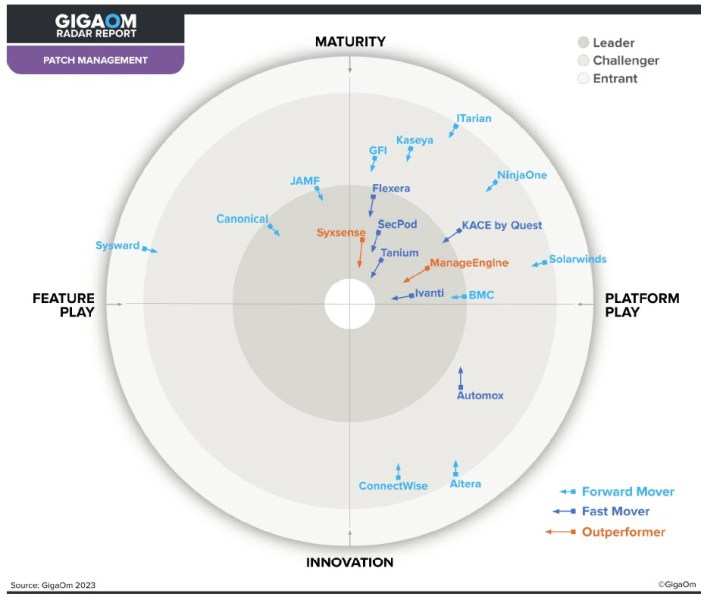
The GigaOm Radar for Patch Management Solutions Report, courtesy of Tanium, highlights the unique strengths and weaknesses of the leading patch management providers. Its timeliness and depth of insight make it a noteworthy report. The report includes 19 different providers.
“CISOs and security leaders need to understand how all of their systems and processes impact their proactive security program,” Eric Nost, senior analyst at Forrester, told VentureBeat. “So my advice is to start with visibility – do you know your environment, the assets that are within it, the control environment, and the impact if these are jeopardized? From there, CISOs can begin to implement a comprehensive prioritization strategy – with patch management and responding to these exposures as the last step.”
“Good patch management practices in the current global environment require identifying and mitigating the root causes responsible for cyberattacks,” said GigaOm analyst Ron Williams. “Patch management also requires the proper tools, processes, and methods to minimize security risks and support the functionality of the underlying hardware or software. Patch prioritization, testing, implementation tracking, and verification are all part of robust patch management.”
Leading vendors include Automox, ConnectWise, Flexera, Ivanti, Kaseya, SecPod and Tanium.
“Our goal is to eliminate Patch Tuesdays. Essentially you’re always staying ahead of your threats and your vulnerabilities by leveraging Tanium’s Autonomous Endpoint Management to do that,” Tanium CEO Dan Streetman told CRN late last year.
Ivanti’s Neurons for Patch Management reflects the future direction of risk management by providing IT and security with a shared platform that prioritizes patching by vulnerability and internal compliance guidelines, along with a centralized patch management system that gives IT and security teams visibility into threats and vulnerabilities.
During a recent interview with VentureBeat, Srinivas Mukkamala, chief product officer at Ivanti, said that “being aware of potential threats posed by vulnerabilities, including those currently being exploited in cyberattacks, aids organizations in taking a proactive rather than reactive approach to patch management.”

The GigaOm Radar plots vendor solutions across a series of concentric rings, with those set closer to the center judged to be of higher overall value. The chart characterizes each vendor on two axes — balancing Maturity versus Innovation and Feature Play versus Platform Play — while providing an arrow that projects each solution’s evolution over the coming 12 to 18 months. Source: GigaOm Radar for Patch Management Solutions Report.
Cunningham’s five-point plan every business can take to improve patch management
VentureBeat recently had the opportunity to sit down (virtually) with Chase Cunningham, a renowned cybersecurity expert who currently serves as vice president of security market research at G2 and is often referred to as Dr. Zero Trust.
Cunningham has more than two decades of experience in cyber defense and is a leading voice advocating for stronger patch management practices. He is also actively involved in assisting a variety of government agencies and private-sector organizations to adopt zero-trust security frameworks. Previous high-profile roles include chief strategy officer at Ericom Software and principal analyst at Forrester Research, where he was instrumental in shaping the industry’s understanding of Zero Trust principles.
When asked for an example of where A.I.-driven patch management is delivering results, Cunningham told VentureBeat, “One notable example is Microsoft’s use of AI to enhance its patch management processes. By leveraging machine learning algorithms, Microsoft has been able to predict which vulnerabilities are most likely to be exploited within 30 days of their disclosure, allowing them to prioritize patches accordingly.” He added, “This approach has significantly reduced the risk of successful cyberattacks on their systems.”
Here is Cunningham’s five-point plan he shared with VentureBeat during our interview recently:
- Leverage AI/ML Tools: To avoid falling behind in patch management, CISOs should invest in AI/ML-powered tools that can help automate the patching process and prioritize vulnerabilities based on real-time risk assessments.
- Adopt a Risk-Based Approach: Instead of treating all patches equally, adopt a risk-based approach to patch management. AI/ML can help you assess the potential impact of unpatched vulnerabilities on your organization’s critical assets, allowing you to focus your efforts where they matter most. For example, vulnerabilities that could lead to data breaches or disrupt critical operations should be prioritized over those with lesser impact.
- Improve Visibility and Accountability: One of the biggest challenges in patch management is maintaining visibility over all endpoints and systems, especially in large, decentralized organizations. AI/ML tools can provide continuous monitoring and visibility, ensuring that no system or endpoint is left unpatched. Additionally, establishing clear accountability within your I.T. and security teams for patching can help ensure that patches are applied promptly.
- Automate Wherever Possible: Manual patching is time-consuming and prone to errors. CISOs should strive to automate as much of the patch management process as possible. This not only speeds up the process but also reduces the likelihood of human error, which can lead to missed patches or incorrectly applied updates.
- Regularly Test and Validate Patches: Even with AI/ML tools, it’s crucial to regularly test and validate patches before deploying them across the organization. This helps prevent disruptions caused by faulty patches and ensures that the patches are effectively mitigating the intended vulnerabilities.
When it comes to patching, the best offense is a good defense
Containing risk starts with a strong patch management defense, one that can flex and adapt as a business changes.
It’s encouraging to see CISOs seeing themselves as strategists focused on how they can help protect revenue streams and contribute infrastructure support to new ones. CISOs are starting to look for more ways they can help drive revenue gains, which is a great strategy for advancing their careers.
The bottom line is that the risk to revenues has never been greater and it’s on CIOs, CISOs, and their teams to get patch management right to protect every existing and new revenue stream.